|
Intel has released a security alert for their management engine interface that is likely to affect all 6th, 7th, and 8th generation of their Core i series CPUs. The summary of the problem that is outlined on Intel's website; Intel® Management Engine (Intel® ME 11.0.0-11.7.0), Intel® Trusted Execution Engine (Intel® TXE 3.0), and Intel® Server Platform Services (Intel® SPS 4.0) vulnerability (Intel-SA-00086) In response to issues identified by external researchers, Intel has performed an in-depth comprehensive security review of the following with the objective of enhancing firmware resilience:
Systems using Intel ME Firmware versions 11.0.0 through 11.7.0, SPS Firmware version 4.0, and TXE version 3.0 are impacted. You may find these firmware versions on certain processors from the:
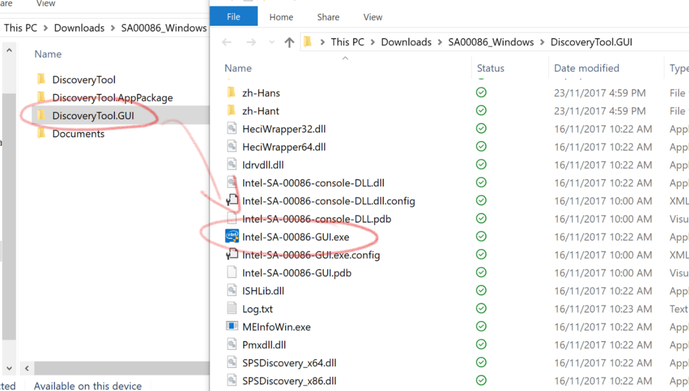
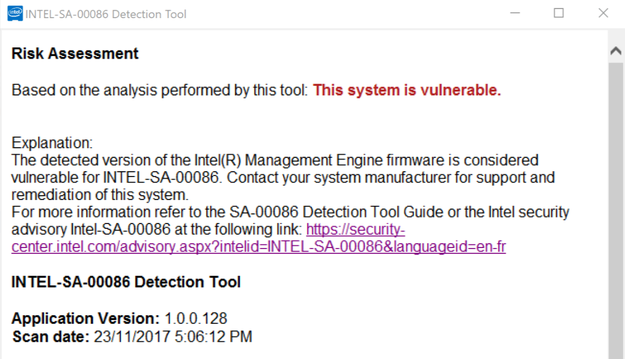
Intel has released a downloadable tool that will help you discover whether your hardware is affected or not. Technical details are also available on their website. Within the zip file download is a GUI tool, running the tool will result in a pass or fail on the vulnerability for the system you run it on. OEM hardware manufacturers will be required to release firmware patches to resolve this issue. For all of our hardware customers; we will be maintaining a set of links on this page for your reference. If you require any support on this issue then please contact our support team or your account manager through your usual channels. For our ongoing SCCM support contract customers, we have already started the update management process and will liaise with you directly on performing updates as they become available. The most up-to-date source for manufacturer's update links is on Intel's website directly; Intel Management Engine Critical Firmware Update (Intel SA-00086) Update 30/11/2017: Direct OEM links to their specific information; In Brief
Researchers have discovered a serious vulnerability in Infineon Trusted Platform Module (TPM) cryptographic processors used to secure encryption keys in many PCs, laptops, Chromebooks and smartcards. In cryptographic terms, the flaw in the way the public key encryption key pair is generated makes it possible for an attacker to work out private 1024-bit and 2048-bit RSA keys stored on the TPM simply by having access to the public key. This would allow an attacker to remove encryption or alter information otherwise protected by the keys stored on the TPM. What is TPM? A TPM is a cryptographic chip built on to the motherboard of many (but not all) PCs and laptops as a secure place to store system passwords, certificates, encryption keys and even biometric data (e.g. for fingerprint login or Windows Hello). The principle is that storing keys inside the TPM is a lot better than keeping them on the hard drive or letting them be managed by the operating system, both of which can be compromised. Microsoft’s BitLocker uses a TPM. They can also be used for authentication (checking a PC is the one it claims to be) and attestation (that a system’s boot image hasn’t been tampered with), for example on Google’s Chromebooks. Remediation for Windows Devices Step 1: Apply all Microsoft Windows Operating System Security Updates Step 2: Determine devices in your organization that are affected using event log entries. NOTE: After the applicable Windows update is applied, the system will generate Event ID 1794 in the Event Viewer after each reboot under Windows Logs - System when vulnerable firmware is identified. On devices running Windows 10 that have the October 2017 security update installed, in a CMD prompt, type "TPM.MSC" to open the Trusted Platform Module (TPM) Management snap-in. Devices with affected TPM modules will display the following error message: (Shown Below)
Step 4: Once the firmware update has been applied to vulnerable devices, additional steps may be required (e.g. devices where BitLocker is in use) Links to firmware updates The best source for up-to-date firmware links appears to be Infineon's website; Information on TPM firmware update for Microsoft Windows Direct manufacturer links from that page are; |
The Laptop CompanyNews and announcements Archives
December 2019
|
Get in touch
|
© COPYRIGHT THE LAPTOP COMPANY (LTD) 2022. ALL RIGHTS RESERVED.
|